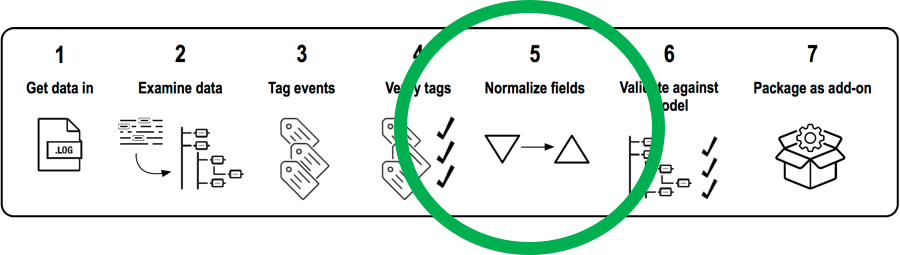
Normalizing Data Fields using Eval and Case
BACKGROUND
Lately I’ve been working with a lot of Windows Security logs with different Event Codes. I wanted to set the field “src_user” but Splunk was auto-extracting field value pairs to other field names. This was particularly frustrating because I wanted to map events with different Event Codes to the same data model. In order to map different fields to “src_user,” I would need to normalize the different field names to “src_user.” Below, I go though an example using a case statement that worked perfectly and may be useful to others who come across a similar issue.
GOAL
I want to extract the “src_user” field from different types of events. In this example, I will be working with an event with Event Code 4727 and an event with Event Code 631. When examining the raw events for both Event Codes, I found that the “Account_Name” field from events with Event Code 4727 and the Caller_User_Name” field from events with Event Code 631 mapped to the “src_user” field.
SOLUTION
EVAL-src_user = case(EventCode=4727,Account_Name,EventCode=631,Caller_User_Name,1==1,src_user)
EXPLANATION
The EVAL case statement above was placed in the props.conf of the Windows TA. The eval expression is using a case statement to set the “src_user” based on the Event Code. The statement looks for an event with Event Code 4727 and sets the “Account_Name” field to “src_user” and is also looking for an event with Event Code 631 and setting the “Caller_User_Name” field to “src_user.” If the event doesn’t have Event Code 4727 or Event Code 631, the expression "1==1" will evaluate to "true" and use the default “src_user” field for all other events.
- Log in to post comments

