BACKGROUND
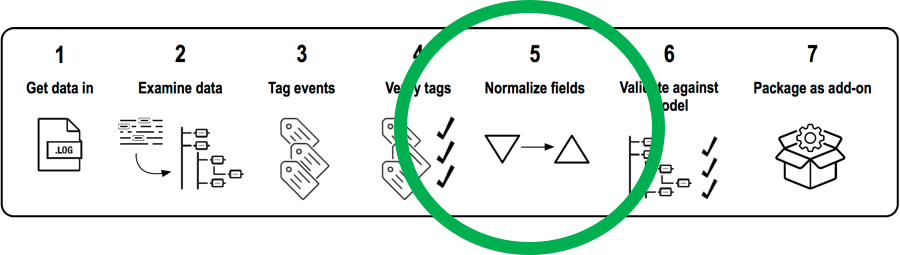
Lately I’ve been working with a lot of Windows Security logs with different Event Codes. I wanted to set the field “src_user” but Splunk was auto-extracting field value pairs to other field names. This was particularly frustrating because I wanted to map events with different Event Codes to the same data model. In order to map different fields to “src_user,” I would need to normalize the different field names to “src_user.” Below, I go though an example using a case statement that worked perfectly and may be useful to others who come across a similar issue.
...